Outrageous Info About How To Detect Buffer Overrun

At a certain point before the.
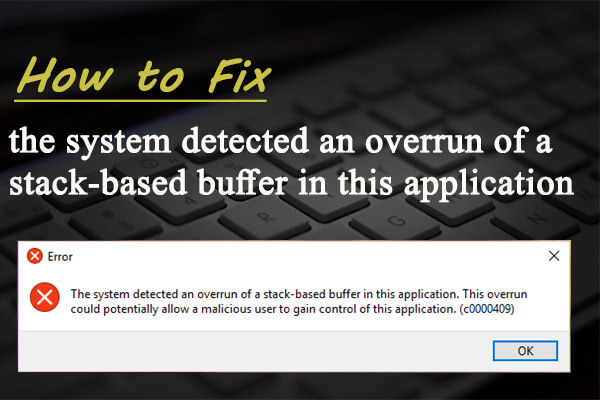
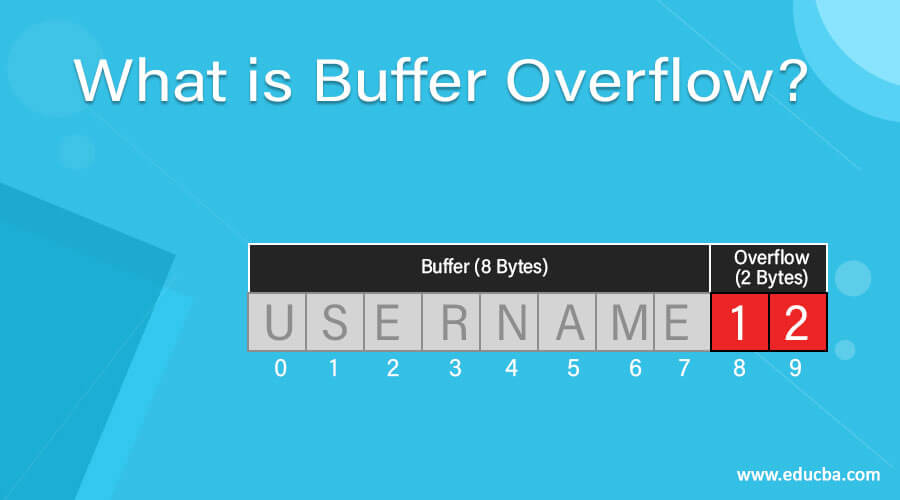
How to detect buffer overrun. Buffer overflow attacks generally need to know where the executable code is located. Windows dev center home ; This causes a bug check when a program tries to access memory beyond its special pool memory.
Using the registry editor to change system settings the registry editor is a tool in windows. You are seeing an improvement to the /gs mechanism, first added to vs2012. A buffer overrun is one of the most common sources of security risk.
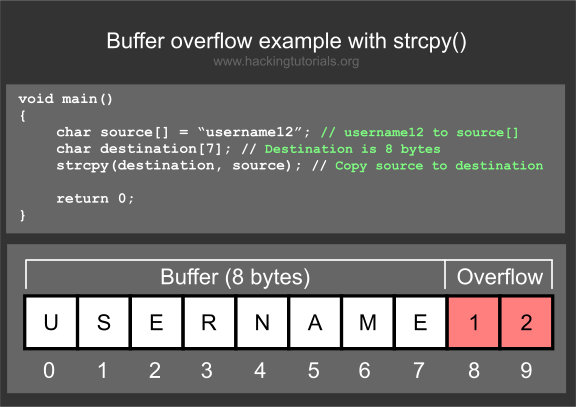
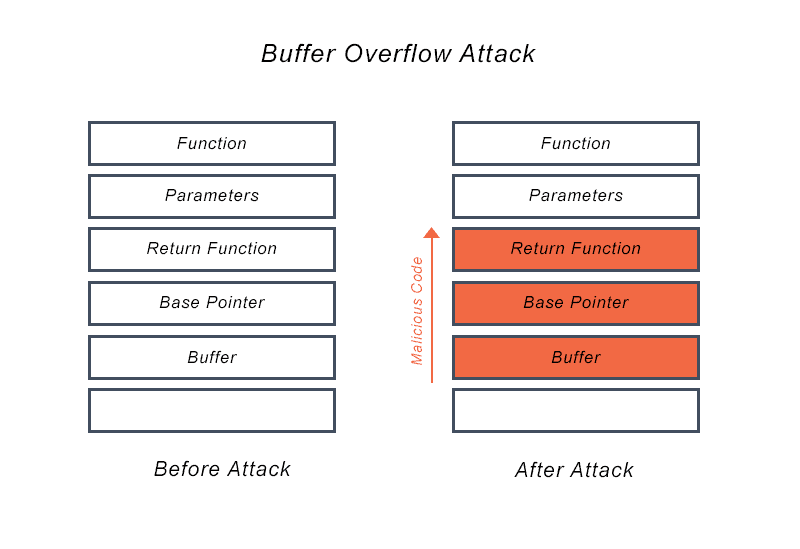
Canaries are inserted at compile time to help detect buffer overflows by inserting a word of data between a buffer and the control data on the stack. A buffer overrun has occurred in programx.exe which has corrupted the program's internal state. In the late 1980s, a buffer overflow in unix’s fingerd program allowed robert t.
A buffer overrun is essentially caused by treating unchecked, external input as trustworthy data. Address space layout randomization (aslr) moves at random around data region locations to. This topic describes how a c/c++ query for detecting a potential buffer.
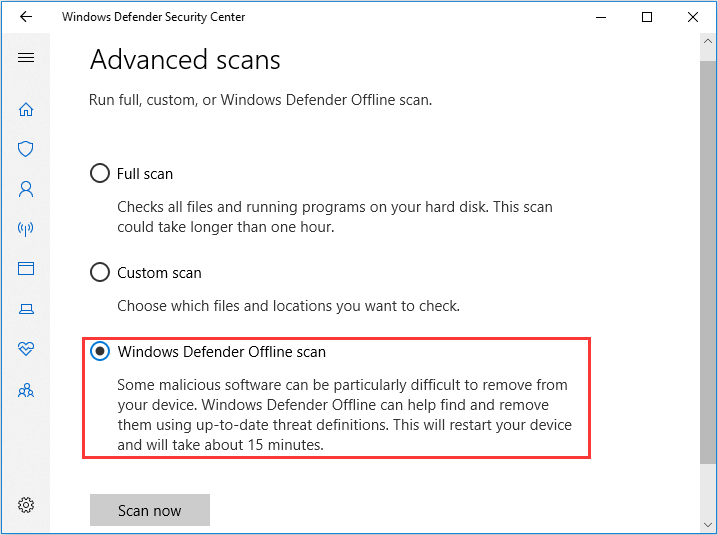
You can use codeql to detect potential buffer overflows by checking for allocations equal to strlen in c and c++. Verify end enables overrun detection on allocations from the special pool. In the configure behavior monitoring dialog box:
According to the msdn library, when you compile c or c++ source code by using the visual c++ 2013 c/c++ compiler, visual c++ 2013 should detect some buffer overrun scenarios (of.